When it comes to keeping your data safe, you want a system you can truly trust. But with so many options out there, how do you know which one offers the best security features?
You need clear answers to protect your personal information and business assets from threats. You’ll discover which system stands out for its strong security and why it might be the perfect fit for your needs. Stay with us to find out how to make the smartest, safest choice for your digital world.
Top Secure Systems
Security is a top priority for many users. Choosing a system with strong protection helps keep data safe. Some systems focus heavily on security features. These systems guard against threats and keep information private.
Below are some of the top secure systems known worldwide. Each offers unique tools to protect users from cyber attacks and data breaches. Understanding their security strengths helps in making a better choice.
Windows Defender Security
Windows includes a built-in security tool called Windows Defender. It provides real-time protection against viruses and malware. The system updates regularly to fight new threats. It also offers firewall controls to block harmful connections.
Macos Security Features
Apple’s macOS has strong security measures. It uses a secure boot process to verify software. The system encrypts data with FileVault to protect files. Apps must get permission before accessing sensitive data.
Linux Security Options
Linux is famous for its security and flexibility. It uses strict user permissions to limit access. Many distributions come with built-in firewalls and antivirus tools. Regular updates fix security vulnerabilities quickly.
Android Security Layers
Android protects devices through multiple security layers. Google Play Protect scans apps for malware. The system enforces app permissions to limit data access. Encryption keeps user data safe on the device.
Ios Security Architecture
iOS is designed with a secure environment for apps. It uses sandboxing to isolate apps from each other. Data is encrypted, and Face ID or Touch ID adds extra protection. Regular updates fix security issues fast.

Credit: en.wikipedia.org
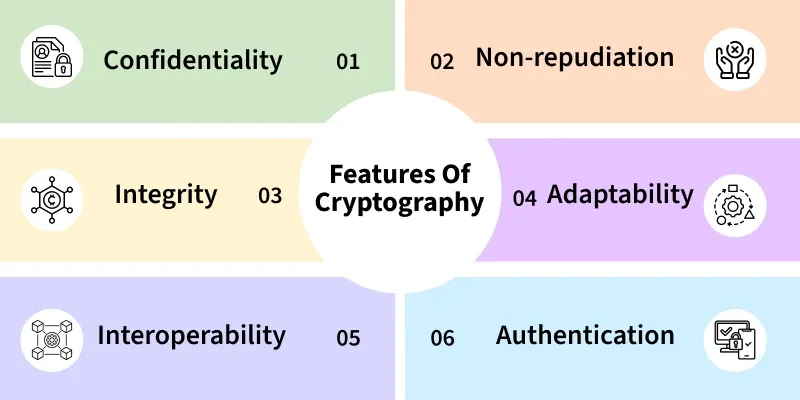
Key Security Features
Security features are the backbone of any system that aims to protect sensitive data and maintain user trust. Understanding the key security features helps you evaluate which system can best safeguard your information. These features work together to create a secure environment, reducing risks and preventing unauthorized access.
Encryption Methods
Encryption scrambles your data so only authorized users can read it. Strong encryption, like AES-256, is widely trusted for protecting information both in transit and at rest.
Think about your emails or files—encryption ensures that even if someone intercepts them, the content remains unreadable. Some systems also use end-to-end encryption, meaning only the sender and receiver can access the data, not even the service provider.
Access Controls
Access controls decide who gets in and what they can do once inside. You want a system that lets you set detailed permissions, limiting users to only the data and functions they need.
This reduces the risk of accidental or malicious data exposure. Role-based access control (RBAC) is a practical example, where users are assigned roles with predefined access rights.
Authentication Protocols
Authentication confirms that users are who they claim to be before granting access. Systems supporting multi-factor authentication (MFA) add an extra layer of security by requiring something you know (password) and something you have (a phone or token).
This combination drastically cuts down the chances of unauthorized access. Have you ever experienced a suspicious login alert? That’s your authentication system working to protect you.
Data Backup And Recovery
Backing up data regularly protects you from data loss due to attacks or accidents. A good system offers automated backups and easy recovery options so you can restore your information quickly.
This means even if something goes wrong, your data isn’t gone forever. How confident would you feel knowing your system can bounce back from a breach or crash without losing critical information?
Operating Systems With Strong Security
In today's digital age, ensuring the security of your operating system is more crucial than ever. With cyber threats constantly evolving, choosing a system with robust security features can make a significant difference in protecting your personal and professional data. Let's dive into some of the operating systems renowned for their strong security capabilities.
Linux
Linux is often lauded for its strong security features, primarily due to its open-source nature. This allows a global community of developers to scrutinize and enhance its security continuously. Have you ever wondered why many servers worldwide run on Linux? It's because of its reputation for reliability and security. Its permission-based architecture ensures that only authorized users can make changes to critical system files, minimizing the risk of unauthorized access.
Windows
While Windows has historically been a target for viruses and malware, recent versions have significantly upped their security game. Windows Defender, Microsoft's built-in security software, provides real-time threat protection. Are you utilizing its features to their full potential? Regular updates and a robust firewall add another layer of security, making it a strong contender in protecting against modern cyber threats.
Macos
macOS is often considered secure due to its Unix-based foundation and Apple's stringent app vetting process. Its Gatekeeper feature ensures that only trusted apps are downloaded and installed. Have you noticed how rarely you hear about macOS-based viruses? This is due to its integrated security features like XProtect, which automatically scans and blocks malware. By keeping your macOS updated, you ensure the latest security patches are applied, safeguarding your system against vulnerabilities.

Credit: www.techprosecurity.com
Security In Cloud Platforms
Security in cloud platforms is a top priority for businesses storing sensitive data and running critical applications. You want a cloud provider that not only protects your information but also complies with industry standards and offers tools to manage risks effectively. Understanding how different platforms handle security helps you choose the best fit for your needs.
Aws Security
AWS offers a strong security framework built on a shared responsibility model. This means AWS manages the security of the cloud infrastructure, while you control security in the cloud, such as configuring firewalls and managing access.
AWS uses advanced encryption methods to protect data at rest and in transit. Tools like AWS Identity and Access Management (IAM) let you control who can access your resources with fine-grained permissions.
One useful feature is Amazon GuardDuty, which continuously monitors your environment for malicious activity. Have you tried setting up GuardDuty alerts? It can quickly notify you of unusual behavior before it becomes a bigger problem.
Microsoft Azure Security
Microsoft Azure focuses heavily on compliance and integrates security across its services. It offers Azure Security Center, which provides a unified view of your security posture and recommendations for improvement.
Azure supports multi-factor authentication and role-based access control to keep unauthorized users out. Plus, its encryption tools cover data both at rest and in motion, ensuring strong protection across the board.
Azure also uses machine learning to detect threats. This proactive approach means you can respond to potential issues before they impact your business. How do you currently monitor your cloud security alerts? Azure’s dashboard can simplify this process.
Google Cloud Security
Google Cloud emphasizes security by design, building protection into every layer. It offers encryption by default, so your data is always protected without extra setup on your part.
Google's Cloud Identity & Access Management (IAM) lets you assign precise permissions, minimizing the risk of accidental exposure. Additionally, Google Cloud’s Security Command Center gives you a central place to view and manage risks.
One feature worth noting is Google's BeyondCorp, which shifts access controls from the network perimeter to individual users and devices. This approach is especially useful if your team works remotely or from multiple locations. What security challenges does your team face when working outside the office?
Mobile Systems Security
Mobile systems have become an essential part of our daily lives, handling sensitive information and personal data. Security in these systems is critical because they are constantly connected to the internet and vulnerable to various threats. Understanding the security features of popular mobile operating systems helps you make smarter choices about your device and how you protect your data.
Android Security Features
Android offers a range of security tools designed to keep your data safe. It uses Google Play Protect, which scans apps for malware before and after you install them.
Another strong point is Android’s frequent security updates, although their delivery depends on your device manufacturer. You can also enable features like:
- Biometric Authentication:Use fingerprint or facial recognition to unlock your device.
- Encryption:Protects the data stored on your device, making it unreadable without your password.
- App Permissions:Control what each app can access, such as your location or contacts.
Have you ever checked which permissions your apps have? It’s worth taking a moment to review and revoke those that seem unnecessary.
Ios Security Features
Apple’s iOS is known for its closed ecosystem, which limits unauthorized app installations, reducing the risk of malware. It also features regular and timely updates that reach all supported devices simultaneously.
iOS includes several built-in protections like:
- Secure Enclave:A dedicated chip that safely stores your biometric data and encryption keys.
- App Store Review:Every app undergoes a strict review process before being available to you.
- Data Protection:Automatic encryption of data when your device is locked.
Have you noticed how your iPhone rarely prompts you about suspicious activity? That’s partly due to these strong security layers working quietly in the background.

Credit: www.techradar.com
Comparing Security Systems
Choosing the right security system means balancing various factors that affect how well it protects your data and devices. Comparing systems helps you see which one fits your needs best, especially when you look closely at their strengths, weaknesses, performance, and ease of use. Let's break down these important aspects to help you make a smart choice.
Strengths And Weaknesses
Every security system has its strong points and drawbacks. Some excel at blocking malware but might struggle with phishing attacks. Others offer excellent encryption but require frequent updates that can be time-consuming.
For example, a system with advanced firewall features might keep hackers out but could be complex to configure for beginners. Do you prefer a system that covers a broad range of threats or one that specializes in specific risks?
Performance Impact
Security systems can affect how smoothly your device runs. Heavy systems might slow down your computer or drain your battery quickly. On the other hand, lightweight solutions often offer less protection but keep your device responsive.
Think about how often you use high-performance applications. Would you accept a slight slowdown for better protection, or do you need a balance that keeps your device fast while still secure?
User Friendliness
A security system’s design can make a big difference in how easily you manage your protection. Some systems offer clear dashboards and simple controls that even beginners can handle. Others require more technical knowledge, which can be frustrating if you’re not familiar with security jargon.
Remember the last time you struggled to set up software? A user-friendly system saves time and reduces mistakes. How much time are you willing to invest learning the ins and outs of your security setup?
Future Trends In System Security
System security is evolving rapidly to fight new digital threats. Future trends focus on smarter, stronger defenses. These trends will shape how we protect data and privacy. Advanced technology plays a key role in this shift. Understanding these trends helps prepare for safer systems.
Ai And Machine Learning
AI and machine learning detect threats faster than humans. They analyze patterns to spot unusual activity quickly. These technologies adapt to new attack methods in real time. AI can reduce false alarms and improve response speed. Many systems now use AI to enhance security layers.
Zero Trust Architecture
Zero Trust means never trust, always verify. Every user and device must prove they are safe. This model limits access to only what is needed. It reduces the risk of insider threats and breaches. Zero Trust is becoming a standard for secure systems worldwide.
Quantum-resistant Encryption
Quantum computers can break today’s encryption quickly. Quantum-resistant encryption uses new math to stop this. It protects data from future quantum attacks. Researchers work to develop and test these new algorithms. This encryption ensures long-term safety for sensitive information.
Choosing The Right Secure System
Choosing the right secure system is key for protecting your data and operations. Security needs differ based on the type of business and how it operates. A system that fits one company might not work for another. It is important to weigh several factors before deciding on a system. These factors help ensure the system meets your security requirements and supports your growth.
Business Needs
Understand what your business requires from a secure system. Identify the type of data you handle and its sensitivity. Consider the number of users and access levels needed. Check if the system supports industry-specific security standards. A system should protect your assets without slowing down work.
Budget Considerations
Set a clear budget for your security system investment. High security often comes with higher costs, but balance is important. Look for systems that offer strong protection within your budget range. Include costs for updates, maintenance, and training. Avoid overspending on features you won’t use.
Scalability
Choose a system that grows with your business. A scalable system adapts to increased users and data volume. It should allow easy upgrades without full replacement. Scalability ensures security stays strong as your company expands. This saves money and effort in the long run.
Frequently Asked Questions
Which System Offers The Strongest Security Features?
Windows, Linux, and macOS all provide strong security features, but Linux is often praised for its robust, customizable security and open-source transparency.
Why Is Linux Known For Superior Security?
Linux’s open-source nature allows constant security audits and quick vulnerability fixes, making it less prone to malware than other systems.
How Does Windows Protect Against Security Threats?
Windows includes built-in antivirus tools like Windows Defender and regular security updates, helping protect users from malware and cyber attacks.
What Security Features Make Macos Reliable?
MacOS uses strong encryption, sandboxing, and regular updates, ensuring data protection and reducing risks from viruses and unauthorized access.
Conclusion
Choosing the best system for security depends on your needs. Some systems offer strong protection for personal data. Others work well for business environments. Think about ease of use and updates. A secure system keeps hackers and viruses away. Regular updates help fix weak spots fast.
Always pick a system known for trust and safety. Your data’s safety matters most. Stay informed and choose wisely to protect yourself.